Cybersecurity • AI Tools • Developer Ecosystem
Vibe Coding, Broken APIs, and Bank Breaches: Is Something Deeper Going On?
Four significant security incidents broke in the span of 72 hours this week Lovable, Notion, Vercel, and Standard Bank. Taken individually, each is notable. Taken together, they paint a picture worth thinking about out loud. Is vibe coding quietly burning down the internet's security posture? Or is something deeper going on? Probably both.
Author: Wilson Kumalo
Category: Cybersecurity & Tech
Reading time: 12 minutes
Published: April 21, 2026
First, Some Context And a Personal Note
I've been quiet on here for a while. The last few months have been a blur working on some things I'll write about eventually, getting through the noise of a tech landscape that feels like it's moving faster than anyone's ability to fully understand it. But every now and then something happens that pulls you back to the keyboard. This week was one of those times.
In the span of roughly 72 hours, four security incidents broke across the internet that, taken individually, are notable. Taken together, they start to paint a picture worth thinking about out loud.
Here's the quick summary of what happened:
- Lovable - An AI app builder left thousands of older projects fully exposed via an unpatched API flaw, leaking source code, database credentials, and customer data. The bug had been reported 48 days prior.
- Notion - Any public Notion page was found to silently leak the names, email addresses, and profile photos of every editor who ever touched it, with zero authentication required. The issue was first reported in 2022.
- Vercel - The frontend cloud platform confirmed a breach via a compromised third-party AI tool, with threat group ShinyHunters allegedly attempting to sell stolen internal data for $2 million.
- Standard Bank (South Africa) - A threat actor publicly released data allegedly exfiltrated from the bank and its insurer Liberty in late February, claiming a 1.2TB haul including over 154 million SQL database rows.
Four incidents. Different targets. Different vectors. But a recurring theme somewhere along the way, someone built or maintained something fast, deployed it confidently, and skipped the part where you think hard about what happens when things go wrong.
The question I keep coming back to: how much of this is the vibe coding era coming home to roost?
What Is Vibe Coding and Why Does It Matter Here?
If you're not familiar with the term, "vibe coding" broadly refers to the practice of building software primarily through AI-assisted generation prompting tools like Lovable, Cursor, Bolt, or Replit Agent to produce functional apps with minimal manual code review. You describe what you want; the AI builds it; you ship it.
At its best, it's genuinely transformative. I've written about this before, AI-assisted development has collapsed the time and cost to ship real products. A solo developer can build what used to take a team. A non-engineer can spin up a working SaaS in a weekend. That's real, meaningful democratisation of software creation.
But here's the trade-off that doesn't get talked about enough: when you're generating code at that speed, with that level of abstraction from the underlying implementation, it's very easy to lose track of what you're actually shipping. Security, in particular, requires a kind of deliberate, adversarial thinking that is almost structurally absent from the vibe coding workflow.
You're not asking "what could go wrong with this API endpoint?" you're asking "does this button do what I want?" Those are very different questions, and only one of them gets asked at vibe-coding speed.
Breach #1: Lovable - The AI That Built the Leak
This one hits differently when you understand what Lovable actually is. It's an AI app builder, you describe what you want to build, the platform generates the code, and you ship. It's the vibe coding stack made product. Thousands of people have used it to build real apps, handling real user data, for real customers.
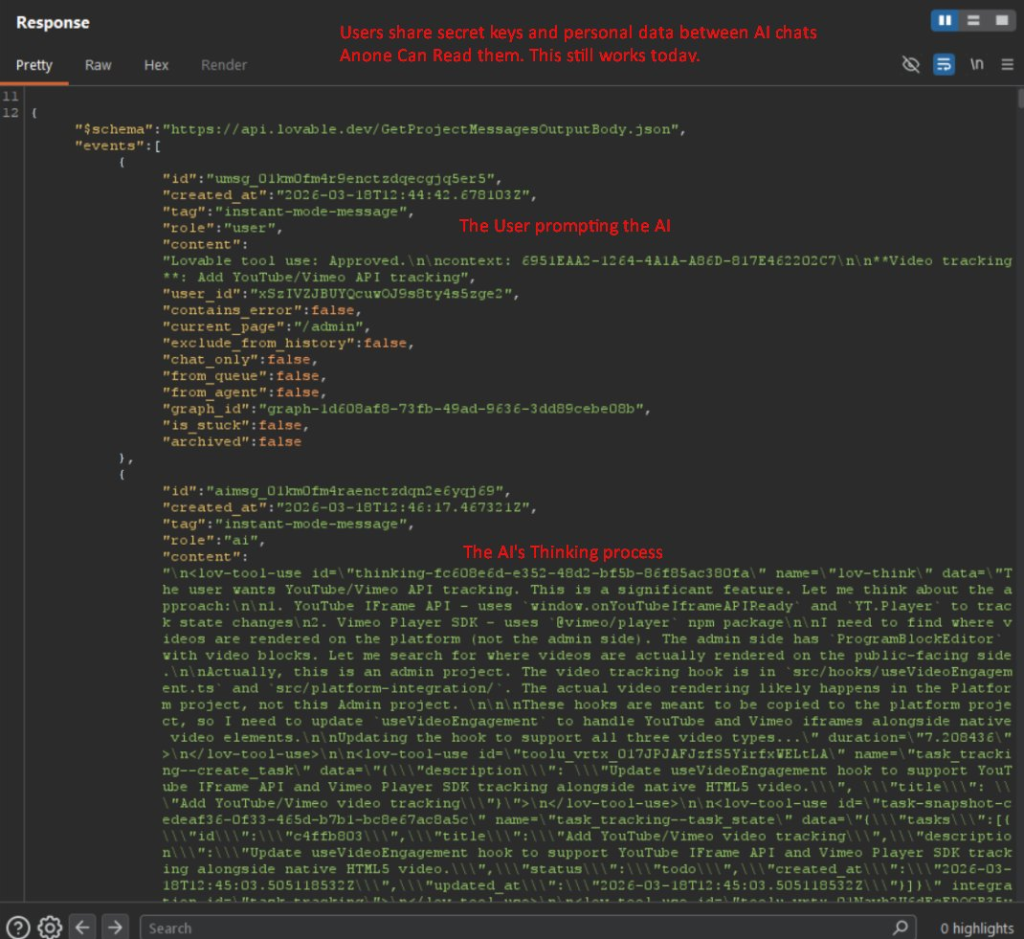
Security researcher @weezerOSINT publicly disclosed that the platform's API handles requests differently depending on when a project was created. New projects those created in April 2026 return a secure 403 Forbidden response to unauthorised users. Projects created before November 2025 return a 200 OK, giving anyone with a free Lovable account complete access to the project's full source tree.
What that means in practice: if you built an app on Lovable before November 2025, even if you've edited it as recently as last week, your project's source code, database credentials, infrastructure secrets, customer information, and full AI chat histories are readable by anyone. No exploit needed. Just an API call.
The researcher demonstrated this by accessing a live admin panel belonging to a real Danish nonprofit, Connected Women in AI. In the exposed AI chat logs, the developer had openly discussed database schemas with the Lovable assistant including table structures storing user emails, names, and other sensitive fields. That's not a theoretical vulnerability. That's a real exposure affecting real people.
What makes this particularly uncomfortable is the dimension of who is affected. Employees from Nvidia, Microsoft, Uber, and Spotify reportedly hold Lovable accounts. If any of them prototyped internal tools before November 2025, those projects may currently be fully readable by the public.
The bug was reported 48 days ago. It was marked as a duplicate and not patched for legacy projects. As of the time of writing, it remains unpatched.
The Vibe Coding Connection
Lovable is literally the vibe coding platform. The irony that the tool enabling AI-generated apps at speed has itself suffered a security failure tied to inconsistent API patching is almost too on-the-nose. But it's also instructive: the same speed and abstraction that makes vibe coding powerful makes security hard to reason about for platform builders and their users alike. When your entire value proposition is "ship in hours not weeks," every incentive in the organisation points away from the slow, deliberate work of adversarial security thinking.
Breach #2: Notion - A Four-Year-Old Problem Nobody Fixed
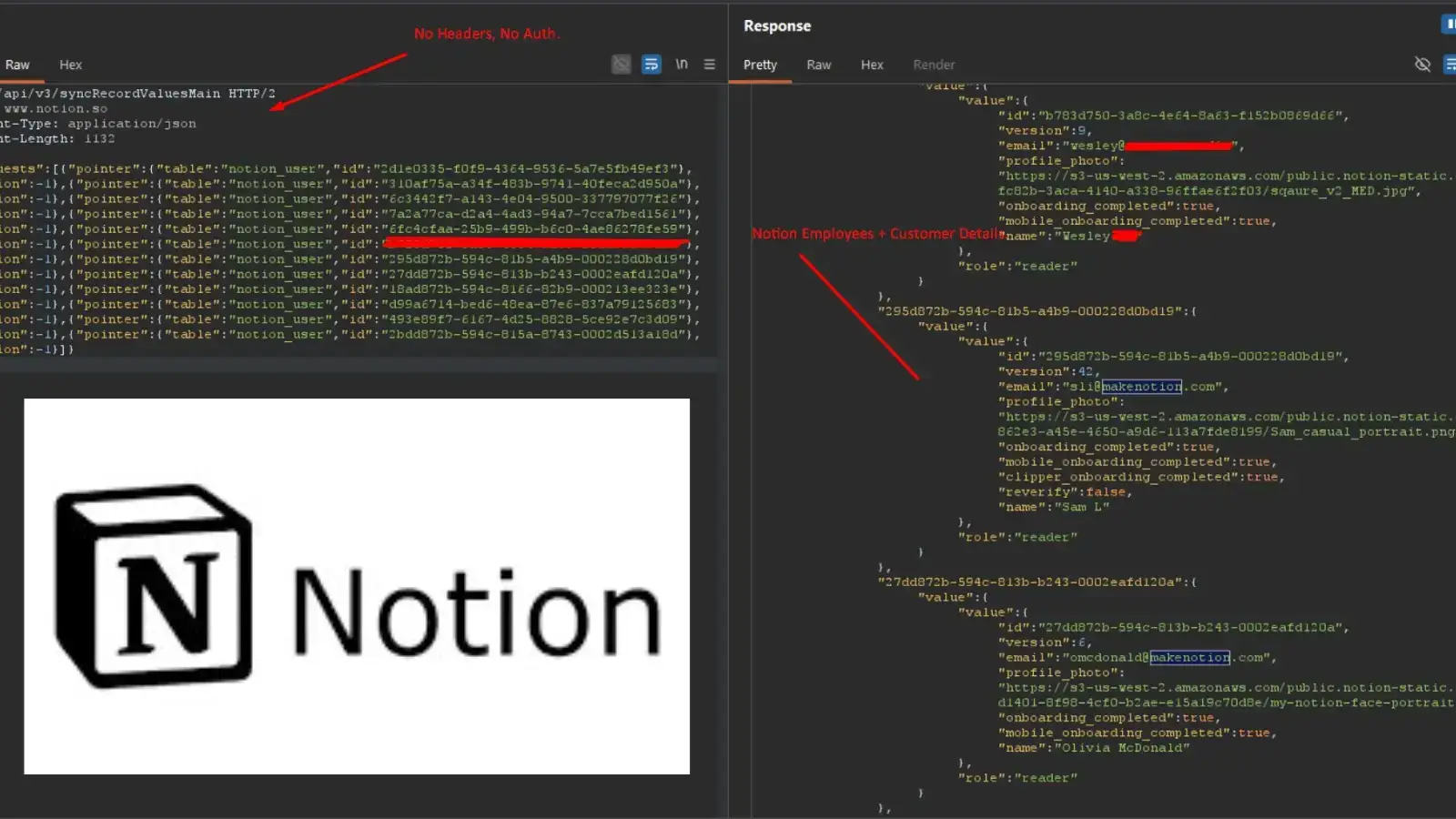
This one is older than the vibe coding era, but it slots neatly into the same story. The vulnerability is deceptively simple: when a Notion page is published to the web, the page source code exposes the Universal Unique Identifiers (UUIDs) of everyone who has ever edited it. Those UUIDs can then be passed to a public API endpoint that requires no authentication whatsoever no cookies, no tokens, nothing and the server responds with the full name, email address, and profile photo of each editor.
The same researcher, @weezerOSINT, demonstrated this publicly and it reignited a conversation that originally happened in mid-2022, when the issue was first submitted to Notion via HackerOne. Notion triaged it as "informative" and took no action. That was nearly four years ago.
For organisations using Notion for public-facing wikis product documentation, team handbooks, onboarding guides this means every employee who has ever touched those pages has had their email exposed to anyone who cared to look. No warning was ever shown in the "Publish to web" dialog. No opt-out was offered. The exposure was silent and persistent.
A Notion employee initially suggested this was documented behaviour users had been warned about before publishing. Researchers quickly disproved this by testing fresh accounts, finding the publish dialog contains no such warning. The employee then acknowledged the current setup is unacceptable and stated that fixes are being explored including either stripping PII from public endpoints entirely, or implementing an email proxy system similar to GitHub's.
The Deeper Problem
This is less about vibe coding and more about how security reports get triaged at scale. "Informative" is a HackerOne status that effectively means: we've noted this, it's not being fixed. That's a policy decision, not a technical one. And for four years, Notion's policy was: the email addresses of your entire team are freely queryable by anyone with internet access, by design.
Security debt doesn't stay still. The exposure grows as the platform grows. At some point the interest always comes due and it usually comes due publicly.
Breach #3: Vercel When Your AI Tool Becomes the Attack Surface

Vercel confirmed a breach in an official security bulletin published April 18–19, 2026. The attack vector is worth paying close attention to: attackers didn't breach Vercel directly. They compromised Context.ai, a third-party AI tool being used by a Vercel employee. Through a malicious Google Workspace OAuth app associated with Context.ai, they hijacked that employee's Workspace account and from there, pivoted into Vercel's internal systems.
The hacker group ShinyHunters posted on BreachForums claiming to have Vercel's internal database, access keys, source code, employee accounts, API keys, and both NPM and GitHub tokens all available for $2 million. As proof, they shared a text file containing 580 Vercel employee records including names, email addresses, account status, and activity timestamps, along with a screenshot of an alleged internal Vercel Enterprise dashboard.
Vercel CEO Guillermo Rauch described the attackers as "highly sophisticated," noting they may have used AI capabilities to accelerate the intrusion. He urged all customers to immediately rotate API keys and tokens as a precaution. The company confirmed that Next.js and its supply chain remain unaffected and all services are operational.
An important technical note: Vercel confirmed that environment variables explicitly marked as "sensitive" which are stored in a manner that prevents them from being read showed no evidence of being accessed. But any variable not marked sensitive and containing secrets like API keys, database credentials, or signing tokens should be treated as compromised and rotated immediately.
The AI Tool Risk Surface
This incident directly implicates the AI tooling layer that most developer teams now run on. The breach didn't start with Vercel it started with an AI tool an employee was using. As developers increasingly plug AI assistants, coding tools, and productivity platforms into their work environments, each of those tools becomes a potential attack surface. The OAuth trust chain just got a lot longer, and most organisations haven't rethought their access hygiene to account for it.
How many AI tools in your stack currently have access to your Google Workspace? How many of those have you audited in the last 30 days?
That's the real question this incident is asking.
Breach #4: Standard Bank Africa's Biggest Bank, Out in the Open
This one is local and it's significant. Standard Bank is one of Africa's largest financial institutions, with operations across 20 countries on the continent and a large retail banking base in South Africa. The breach was originally disclosed on 23 March 2026, with the bank communicating that an incident had involved unauthorised access to select data. Updates followed on 2 April and 13 April.
Then this week, the data went public.
A threat actor called Rootboy claimed online that access to Standard Bank and Liberty's systems was gained in late February, and maintained for just over three weeks. During that time, the actor claims to have moved laterally across SharePoint, OneDrive, Power Apps, App Dynamics, Jira, Confluence, Citrix, Remedy, and both Microsoft and Oracle SQL databases. The claimed exfiltration totals 1.2 terabytes of data and approximately 154 million SQL database rows.
Standard Bank has confirmed the affected systems were internal administrative and document filing systems not the core transactional banking platform, which it says remained secure throughout. The data confirmed to be involved includes names, ID numbers or registration numbers, contact details (phone, physical and email addresses), account numbers, and BBBEE categorisation and VAT registration numbers.
The bank says it has implemented enhanced credit bureau monitoring, additional transaction monitoring, and expanded fraud detection across its platforms in response. It has complied with applicable regulatory notification requirements and is cooperating with the relevant authorities. The Information Regulator has confirmed it still needs further information from Standard Bank and Liberty to carry out a thorough investigation.
Why This Matters Beyond South Africa
The real risk for affected customers isn't someone emptying your account the transactional systems are reportedly intact. The risk, as security experts have noted, is the downstream phishing wave that reliably follows large data releases. When attackers have your name, ID number, contact details, and account number, they can construct highly personalised social engineering attacks that are genuinely difficult to detect.
In South Africa, where mobile banking adoption is high, these attacks tend to arrive via SMS, WhatsApp, or direct phone calls rather than email and they tend to work. If you bank with Standard Bank, the most important thing you can do right now is treat any unexpected contact referencing your banking details with deep suspicion, no matter how official it sounds. Verify through trusted channels only.
So What's Actually Going On?
It would be convenient to pin all of this on vibe coding and call it a day. Build fast, skip security, pay later that's a clean narrative. And there's truth in it, particularly for the Lovable story.
But the Notion bug is four years old. The Standard Bank breach was executed over three weeks of patient, methodical movement through internal systems that's not a vibe coder's mistake, that's a sophisticated threat actor doing real work. The Vercel breach came through OAuth supply chain compromise, a vector that predates AI app builders by years.
What I think is actually happening is a convergence of several things at once:
1. The AI Tool Stack Is Now a Primary Threat Surface
Vercel's breach started at an AI tool. Lovable is the AI tool. We're granting these platforms deep access to our codebases, credentials, and workspaces and most of us are doing it without the kind of access review we'd apply to a new engineer joining the team. Sophisticated attackers are actively exploiting this gap. The Vercel CEO noted the attackers may have used AI themselves to accelerate the intrusion. The same democratisation that lets a solo developer ship faster lets a threat actor move through systems faster.
2. Vibe Coding Externalises Security Thinking
When you generate code rather than write it, you can't easily reason about what it does under adversarial conditions. You can ask an AI to build you an authentication system, and it'll produce something that works and it might have no rate limiting, inconsistent access checks, or hardcoded secrets. The AI won't flag these unless you ask the right questions. At vibe-coding speed, most people aren't asking those questions.
3. Security Debt Compounds Silently and Fast
The Notion story illustrates this perfectly. A 2022 bug triaged as "informative" sits unpatched for four years. The exposure grows as the platform grows. Millions of public pages continue leaking editor emails to anyone who wants them, and nobody notices until a researcher makes it viral on Twitter. Security debt doesn't announce itself it accumulates quietly until it doesn't.
4. The Threat Actor Capability Curve Is Steepening
Rootboy spent three weeks moving methodically through Standard Bank's internal systems across SharePoint, Jira, Oracle SQL, and more before extracting 1.2TB. ShinyHunters compromised an AI tool's OAuth chain to pivot into a Fortune 500 infrastructure provider. These aren't unsophisticated attacks. The tools available to threat actors including, reportedly, AI are improving alongside the tools available to defenders. The asymmetry tends to favour attackers.
What Should You Actually Do?
I'm not going to wrap this with a generic "patch your software" bullet list. But there are a few things worth actually acting on in light of this week:
If You Build With AI Tools
Treat generated code as untrusted until reviewed. Specifically prompt your AI assistant about the security implications of what it builds it will often surface issues it wouldn't flag unprompted. If you're using Lovable, Bolt, or similar: audit what's in your project, who has access, and whether any secrets are stored in ways that could be exposed through an API endpoint.
Audit Your OAuth Grants Today
The Vercel breach started at an OAuth-connected AI tool. Go into your Google Workspace, GitHub, and other connected platforms and look at what third-party apps currently have access. Remove anything you no longer use or don't recognise. This takes ten minutes and is genuinely worth doing now, not next sprint.
If You're a Standard Bank Customer
Change your digital banking passwords. Enable biometric authentication on the mobile app. Be deeply sceptical of any unsolicited contact calls, SMS, WhatsApp that references your personal or account details, regardless of how official it sounds. The bank's fraud line is 0800 222 050 for South Africa-based customers.
For Notion Users
Audit which pages in your workspace are published to the web. Unpublish anything that doesn't strictly require public access. Until Notion deploys a fix, any published page exposes the email addresses of its editors so reduce the footprint wherever you can.
Conclusion: What's Real, What's Broken, and What's Next
The Four Incidents at a Glance
- 🔴 Lovable API flaw exposing pre-November-2025 projects; unpatched as of writing despite 48-day-old report
- 🟠 Notion Editor emails exposed on all public pages via unauthenticated API; known since 2022, fix in progress
- 🔴 Vercel Confirmed breach via compromised AI tool OAuth chain; ShinyHunters claiming $2M sale of internal data
- 🔴 Standard Bank Stolen data publicly released; 1.2TB claimed, ~154M SQL rows, phishing risk now elevated for SA customers
The Bigger Picture
The week's incidents revealed something important: the infrastructure of the modern developer ecosystem AI app builders, productivity platforms, frontend cloud providers, third-party tooling has grown faster than the security thinking around it. That gap is now being actively exploited.
Vibe coding isn't the villain here. Neither is AI tooling. Used thoughtfully, both are genuinely powerful. But "move fast and ship" is a disposition that needs to be actively counterbalanced by "now let's think about what breaks." The incidents this week are, among other things, a reminder that the counterbalancing part doesn't happen automatically and when it doesn't happen, eventually someone else does it for you.
It's good to be writing again. Things are interesting out here sometimes in ways that feel a little too interesting. More soon.
Wilson

